SBOM Security: Fortifying Your Software Supply Chain in 2026
In 2026, the digital landscape faces unprecedented cyber threats, with software supply chain attacks escalating by an estimated 30% year-over-year. Understanding and implementing Software Bill of Materials (SBOM) security is no longer optional; it’s a critical defense mechanism. An SBOM is a nested inventory of all the components, libraries, and dependencies that make up a piece of software. By detailing these elements, SBOMs provide transparency into the software supply chain, enabling organizations to identify and mitigate potential security risks before they are exploited. This detailed inventory is the first step in a robust security strategy, allowing for proactive vulnerability management and compliance adherence.
What is a Software Bill of Materials (SBOM)?
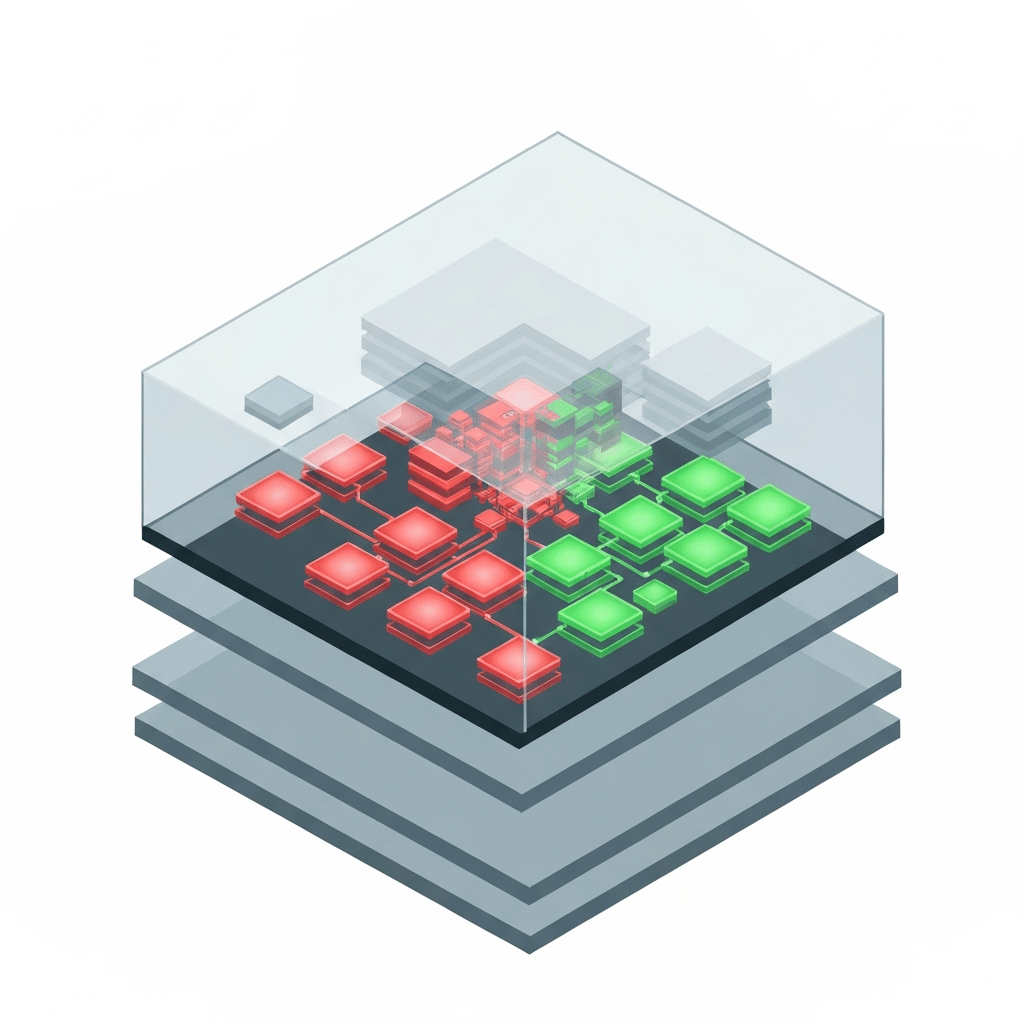
A Software Bill of Materials (SBOM) is a formal, machine-readable inventory that lists all the components, including open-source and commercial software, that are present in a software product. Think of it as an ingredient list for your software. It details not only the direct components but also their transitive dependencies – the libraries that your libraries rely on. This comprehensive list is essential for understanding the composition of software and managing associated risks.
Why is SBOM Security Crucial?
The increasing reliance on open-source software has expanded the attack surface for many organizations. A single vulnerable component within a complex software system can lead to a catastrophic breach. SBOM security addresses this by providing the visibility needed to track and manage these components effectively. Without an SBOM, identifying all instances of a vulnerable library across an organization’s software portfolio can be an overwhelming, if not impossible, task. This lack of visibility leaves organizations susceptible to supply chain attacks, where malicious actors inject compromised code into legitimate software updates.
For example, the SolarWinds attack in 2020, a prime example of a devastating supply chain compromise, highlighted the urgent need for better software supply chain security. While not directly an SBOM failure, the incident underscored how a breach in one part of the supply chain could impact thousands of downstream users. SBOMs aim to prevent such widespread damage by offering a clear map of software components.
Key Components of an Effective SBOM
An effective SBOM should provide granular details about each software component. These details typically include:
- Component Name: The official name of the software component.
- Version: The specific version number of the component.
- Supplier Name: The entity that created or supplied the component.
- Unique Identifiers: Such as CPE (Common Platform Enumeration) or PURL (Package URL), which help in unambiguous identification.
- Relationship Data: How components relate to each other within the software build.
- License Information: Details about the open-source licenses associated with each component, crucial for legal and compliance reasons.
Vulnerability Data: While not always generated within the SBOM itself, it’s the primary data point used to correlate* with vulnerability databases.
These elements combine to create a comprehensive picture of the software’s makeup, enabling security teams to act decisively.
How Does SBOM Security Enhance Vulnerability Management?
SBOM security directly bolsters vulnerability management by enabling rapid identification of affected systems. When a new vulnerability is discovered in a widely used open-source library, organizations with SBOMs can quickly query their inventory to determine which of their applications use that specific vulnerable component. This allows for targeted patching and remediation efforts, significantly reducing the time window for attackers to exploit the vulnerability.
Consider the Log4Shell vulnerability discovered in late 2021 affecting the Log4j Java logging library. Organizations that had SBOMs in place were far better equipped to identify their vulnerable systems and prioritize patching compared to those without. This proactive approach minimizes the potential impact of zero-day exploits.
The Role of SBOMs in Compliance and Regulation
Regulatory bodies worldwide are increasingly mandating SBOMs. For instance, the U.S. Executive Order 14028, “Improving the Nation’s Cybersecurity,” issued in 2021, requires software producers selling to the U.S. federal government to provide an SBOM. This regulatory push underscores the growing importance of SBOMs as a standard for software security and transparency.
Compliance with these regulations ensures that organizations are meeting baseline security requirements and demonstrating a commitment to secure software development practices. Furthermore, many industry-specific standards are beginning to incorporate SBOM requirements, making them a cornerstone of modern cybersecurity compliance.
Generating and Managing SBOMs
Generating SBOMs can be achieved through various methods, often integrated into the software development lifecycle (SDLC).
- Build-Time Generation: Tools can automatically generate SBOMs during the software build process by analyzing the declared dependencies in build scripts and package manager manifests.
- Runtime Analysis: Tools can scan running applications or deployed systems to identify components and their versions.
- Manual Creation: While less scalable, manual documentation can be used for simpler software or specific components.
Effective SBOM management involves storing, querying, and regularly updating these inventories. Centralized repositories and integration with security tools are key to leveraging SBOM data efficiently. For organizations using GitHub, tools like Announcing General Availability Of Github Advanced Security For Azure Devops can help streamline the generation and management of SBOMs within their development workflows.
SBOM Formats: SPDX and CycloneDX
Two prominent standards for SBOM formats are Software Package Data Exchange (SPDX) and CycloneDX.
- SPDX (Software Package Data Exchange): Developed by the Linux Foundation, SPDX is an open standard designed to provide a flexible way to contain information about software packages, including copyright, licenses, and security-related information. It aims to facilitate easier and more automated compliance and security processes.
- CycloneDX: An OWASP (Open Web Application Security Project) flagship project, CycloneDX is a lightweight SBOM standard designed for use in application security contexts and supply chain component analysis. It is particularly well-suited for continuous integration/continuous delivery (CI/CD) pipelines.
Both formats serve the purpose of standardizing SBOM data, enabling interoperability between different tools and organizations. The choice between them often depends on existing toolchains and specific organizational needs.
Integrating SBOMs into the SDLC
Integrating SBOM generation and analysis into the Software Development Lifecycle (SDLC) is crucial for maximizing their security benefits. This means creating SBOMs early and often, ideally at every build.
- Development Phase: Developers declare dependencies. Tools can capture these declarations to start building the SBOM.
- Build Phase: Automated tools generate a comprehensive SBOM for the build artifact, including transitive dependencies.
- Testing Phase: SBOM data can be used to identify components with known vulnerabilities that might impact testing.
- Deployment Phase: The SBOM accompanies the deployed software, allowing operations teams to understand its composition.
- Maintenance Phase: As new vulnerabilities are discovered, the SBOM is cross-referenced to identify affected versions and guide patching.
This continuous integration ensures that security teams have up-to-date information about the software they are managing.
Challenges in SBOM Implementation
Despite the clear benefits, implementing SBOM security presents several challenges:
- Tooling Maturity: While improving rapidly, the tooling for SBOM generation and analysis is still evolving. Ensuring accuracy and comprehensive coverage across diverse technology stacks can be difficult.
- Data Accuracy and Completeness: SBOMs are only as good as the data they contain. Inaccurate or incomplete SBOMs can lead to a false sense of security.
- Scalability: Managing SBOMs for a large number of applications and components requires robust infrastructure and efficient processes.
- Operational Integration: Integrating SBOM data into existing security workflows, such as vulnerability scanning and incident response, requires effort and adaptation.
- Legacy Systems: Generating SBOMs for older, less-documented software can be particularly challenging.
Addressing these challenges requires a strategic approach, investment in appropriate tools, and a commitment to process improvement.
The Future of SBOM Security
The future of SBOM security is bright, with ongoing advancements in automation, standardization, and integration. We can expect:
- Wider Adoption: Increased regulatory pressure and industry best practices will drive broader adoption of SBOMs across all sectors.
- Enhanced Automation: AI and machine learning will play a greater role in automating SBOM generation, analysis, and vulnerability correlation.
- Real-time Monitoring: SBOMs will become more dynamic, enabling near real-time monitoring of software supply chain risks.
- Interoperability: Greater standardization will improve interoperability between different SBOM tools and platforms.
- Focus on Provenance: More emphasis will be placed on the origin and integrity of software components, further securing the supply chain. Initiatives like The Github Security Labs Journey To Disclosing 500 Cves In Open Source Projects demonstrate the proactive security efforts being made in the open-source community, which directly benefits SBOM accuracy.
FAQ Section
What is the primary benefit of using an SBOM?
The primary benefit of using an SBOM is enhanced visibility into the software supply chain. This transparency allows organizations to quickly identify all components within their software, track their versions, and understand potential security risks associated with them, thereby improving vulnerability management and compliance.
How do SBOMs help in managing open-source risks?
SBOMs help manage open-source risks by providing a detailed inventory of all open-source components and their dependencies. When a vulnerability is discovered in an open-source library, organizations can use their SBOMs to pinpoint exactly which applications are affected, enabling rapid and targeted remediation efforts.
Are SBOMs legally required?
In many cases, yes. Regulations like the U.S. Executive Order 14028 now mandate SBOMs for software sold to the federal government. Additionally, various industry standards and contractual agreements are beginning to require them, making SBOMs increasingly a legal and contractual necessity.
What are the main formats for SBOMs?
The two most prominent formats for SBOMs are SPDX (Software Package Data Exchange) and CycloneDX. Both are open standards designed to provide a consistent and machine-readable way to represent software component information, including licenses and dependencies.
Can SBOMs prevent all software supply chain attacks?
No, SBOMs cannot prevent all software supply chain attacks on their own. However, they are a critical tool for mitigating the impact of such attacks by providing the necessary visibility to quickly identify and respond to compromises within the software supply chain. They work best as part of a broader security strategy.
Who is responsible for creating an SBOM?
The responsibility for creating an SBOM typically lies with the software producer or developer who builds the software. This includes both in-house development teams and third-party vendors. The goal is to ensure that the SBOM accurately reflects the final software product delivered to the consumer.
Conclusion
In 2026, SBOM security stands as a foundational element of a resilient cybersecurity posture. By providing an accurate and comprehensive inventory of software components, SBOMs empower organizations to navigate the complexities of the modern software supply chain with confidence. They enable proactive vulnerability management, streamline compliance efforts, and build trust between software producers and consumers. While challenges remain in widespread adoption and effective management, the ongoing advancements in tooling and standardization, coupled with increasing regulatory and market demands, ensure that SBOMs will continue to play an indispensable role in securing the digital world. Embracing SBOMs is not merely a technical requirement; it is a strategic imperative for safeguarding against the ever-evolving threat landscape.


